Prior to the pandemic that affects the world since earlier last year, many sectors were already redesigning their operating models to enhance efficiency and effectiveness in the digital era. These efforts are now even more relevant than ever as companies require leaner, more adaptive digital enterprises that can change and respond quickly. We see that transitioning certain functions to cost effective shared service centre or outside the enterprise entirely via managed service or outsourcing relationships with third parties are high on the list of many enterprises planned actions in the Post Pandemic Era.
Many organisations (user entities) are able to function more efficiently and effectively by outsourcing tasks or entire functions to another organisation (service organisation). A service organisation is organised and operated to provide user entities with the benefits of the services of its personnel, expertise, equipment and technology to help accomplish these tasks or functions. Some common outsourced services include customer support, enterprise IT outsourcing services and financial technology (FinTech) services such as online payment mechanism. Other businesses (business partners) enter into agreements with a service organisation that enable the service organisation to use or leverage their services or assets (IP), for example IBM providing hardware and software to a data centre.
These outsourcing relationships may increase revenues, expand market opportunities, and reduce costs for the user entities and business partners, they also result in additional risks arising from interactions with a service organisation and its systems such as matters related to security, availability, integrity, confidentiality and privacy. Both user entities and the business partners would like to understand the effectiveness of controls implemented by the service organisation to meet the excepted services level of user entities and to protect the business partners’ IP.
In supporting their risk assessments on service organisations, user entities and business partners may request independent reports on an examination or review of controls from the service organisation. This is where assurance standards for reporting on service organisation controls such as SOC Reporting and ISAE 3402 were developed.
The Attestation Standards
SOC Reporting was actually not a new development. In the 1990’s, a service auditor's examination performed in accordance with Statement on Auditing Standards (SAS) 70 represents that a service organisation has been through an in-depth examination of their control objectives and control activities, which often include controls over information technology and related processes. In 2011, in conjunction with the release of SSAE 16, the AICPA replaced the service auditor’s examination (SAS 70) report prescribed by SAS 70 with the Service Organisation Controls (SOC) suite of reports.
In April 2016, the AICPA published Statement on
Standards for Attestation Engagements 18; Attestation Standards: Clarification and Recodification in response to "concerns over the clarity, length, and complexity of its standards", with most sections becoming effective on 1 May 2017. SSAE No. 18 supersedes and integrates prior related SSAE releases into a single clarified standard. AICPA also redefined the SOC acronym to System and Organisation controls (SOC) to refer to the suite of services that auditors (CPA firms) could provide for other type of organisations in addition to services organisations, on either system-level or entity level controls of such organisations.
SSAE 18 attestation standards provide for 3 types of services – examination, review (limited assurance) and agreed-upon on procedures engagements. SSAE 18 restructures the attestation standards for the AT-C sections to be applied to particular engagement depends on the type of services provided and the subject matter of the engagement. AC-T section 105 contains requirements and guidance applicable to any attestation engagement. The AT-C section 205 include provisions for Examination Engagement, AT-C section 210 for Review Engagement and AT-C 215 for Agreed-Upon Procedures Engagements.
The SOC reports also prescribes two types of reports on the controls at a service organisation. They are Type 1, which includes an assessment of internal control design, and Type 2, which additionally includes an assessment of the operating effectiveness of controls.
Convergence of Standards
The US Auditing Standards Board (ASB)’s general strategy to coverage its standards with those of the International Auditing and Assurance Standards Board (IAASB). The foundation for AC-T sections 105, 205 and 210 is ISAE 3000,
Assurance Engagements Other than Audit or Reviews of Historical Financial Information. Many of the paragraphs in SSAE 18 have been converged with related paragraphs in ISAE 3000.
ISAE 3402,
Assurance Reports on Controls at a Service Organisation deals with assurance engagements undertaken by an auditor to provide a report for use by user entities and their auditors in the controls at a service organisation as it relates to financial reporting. In SOC terms, ISAE 3402 is SOC 1.
Types of SOC Reporting
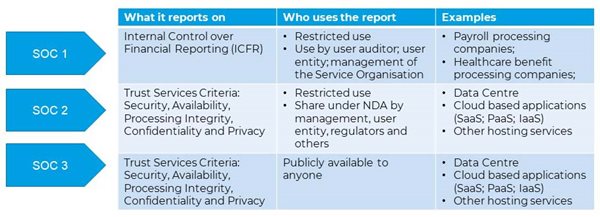
There are also different types (natures) of SOC Reporting, they are SOC 1 (ICFR), SOC 2, SOC 3 and SOC for Cybersecurity.
SOC 1 focuses on controls relevant to internal control over financial reporting (ICFR) of service organisations that may provide services that are relevant to their customers’ (user entities’) internal control over financial reporting and therefore, to the audit of financial statements. For example, a payroll processor who processes payroll for user organisations and provides reports for them to record the related financial transactions. Other examples include healthcare claims processing companies, and custodians for investment companies.
For SOC 2, it focuses on reporting on controls at a service organisation relevant to the AICPA’s Trust Services Criteria of Security, Availability, Processing Integrity, Confidentiality, and or Privacy for specific (knowledgeable) users. Knowledgeable users have understanding of the service organisation’s business, its internal controls and their limitations. Some examples include customers of IT infrastructure management and data centre hosting services. The following is a summary of the 5 Trust Services Criteria:
- Security - Information and systems are protected against unauthorised access, unauthorised disclosure of information, and damage to systems that could compromise the other criteria.
- Availability - Information and systems are available for operation and use to meet the entity’s objectives.
- Processing integrity - System processing is complete, valid, accurate, timely, and authorised to meet the entity’s objectives.
- Confidentiality - Information designated as confidential is protected to meet the entity’s objectives.
- Privacy - Personal information is collected, used, retained, disclosed, and disposed of to meet the entity’s objectives.
SOC 3 is similar to SOC 2 on controls relevant to the Trust Services Criteria. The SOC 3 report only provides limited information on the narrative and design of systems for “General Use” such as for distributing to potential clients and posting on the service organisation’s website. SOC for Cybersecurity focuses on an entity’s cybersecurity risk management programme, its designs, implementation, and operation of cybersecurity controls. The following table depicts the differences between SOC 1, SOC 2 and SOC3:
 A Further Discussion of SOC 2 Reporting
A Further Discussion of SOC 2 Reporting
As SOC 2 (Type 2) Reporting on examination of controls at a service organisation is the most common among the different types of SOC Reporting, this section provides more detail information related to SOC 2 Reporting.
A SOC 2 report does not have to address all 5 Trust Services Criteria, it can address any of the criteria that are most relevant to the service organisation, with security usually as the baseline and add other criteria depending on the industry norms and or preferences and expectations of users of the SOC 2 report. Often for first year audit, it is recommended to only include the security criterion for getting familiar to SOC 2 reporting, and overtime to include other criteria if relevant. For example, availability would be another critical criterion for data centre operations. And regard to the systems in scope, SOC 2 reporting also provides flexibility, the service organisation could define the specific information systems, applications and or services for the reporting. It could be the entire company, a business unit or a function within the organisation. With the scoping, the service organisation would be required to define the in-scope systems and provide descriptions covering the following 5 areas:
- Infrastructure - The physical and hardware components of the systems (facilities, equipment, and networks).
- Software - The programmes and operating software of the systems (systems, applications and utilities).
- People - The personnel involved in the operation and use of the systems (developers, operators, users).
- Procedures - The programmed and manual procedures involved in the operation of the systems (automated and manual).
- Data - The information used and supported by the systems (transaction streams, files, databases).
SOC 2 Audit Process
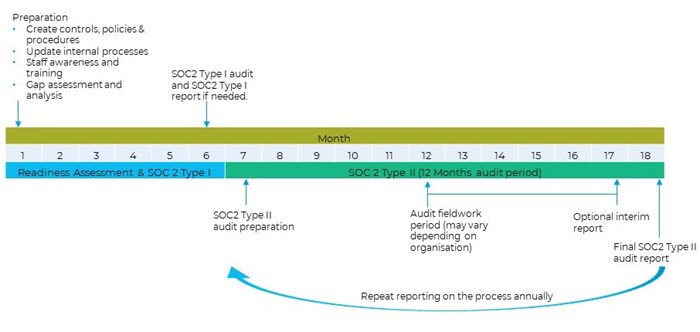
The SOC 2 audit process usually includes 3 steps; the first step is a readiness assessment to identify the gaps in meeting the requirement of the relevant Trust Services Criteria, in order for the service organisation to have an understanding of the issues and to rectify the gaps before the actual audit. After rectifying the identified gaps, the service organisation would be ready for the actual SOC 2 audit. The following diagram illustrates the process:
 Typical Timeline for SOC 2 Reporting
Typical Timeline for SOC 2 Reporting
It is not uncommon for the first SOC 2 (Type 2) Reporting to take about 18 months, in particular when the design and operation of the controls in place are not effective to meet the Trust Services Criteria. It may take up to 6 months to complete the readiness assessment and to rectify the identified issues. In a Type 2 report, as it includes an assessment of the operating effectiveness of controls which involves testing of sample data of a period, usually a 12 months’ period. For Type 1 report as it only includes assessment of design of controls, but not the operating effectiveness of the controls, SOC 2 (Type 1) reporting could be conducted after the readiness assessment phase. See below diagram that illustrates the typical timeline of SOC 2 Reporting.
 Audit Fee for SOC 2 Reporting
Audit Fee for SOC 2 Reporting
The fee for delivering SOC 2 reporting varies from organisation to organisation. Some of the major factors that affects the fee are:
- Size and complexity of the organisation;
- Number of employees;
- Number of locations;
- Trust Services Criteria selected;
- Type of report selected – i.e. Type 1 or Type 2 reports;
- Period covered by the report (i.e. 6 or 12 months); and
- Scope and number of controls of the information system.
As SOC 2 (Type 2) reporting is an annual recurring report as it includes the operating effectiveness of controls of a particular period, the first year audit fee is usually higher due to initial efforts in understanding, documenting and testing the controls. In subsequent years, the service organisation can expect the audit fee will be reduced, if the reporting scope remains unchanged.
SOC Reporting in Asia Pacific
In Asia Pacific (APAC), you can see a proliferation of call centres, software development centre, business process outsourcing and data centres. According to GlobalData’s Market Opportunity Forecasts Model, APAC is set to emerge as the second largest BPO market globally, behind North America (US$152.5bn). The overall BPO market in the region is estimated to grow at a compound annual growth rate (CAGR) of 10% between 2018 and 2023 to reach US$120.4 billion. A 2019 Cushman & Wakefield’s report also indicated the total market size for Asia Pacific co-location data centres is forecast to be around US$28 billion by 2024, 20 per cent higher than the US$23.4 billion market size projected for North America. The need of SOC Reporting will grow exponentially in Asia Pacific in the post pandemic era.